
There is No Such Thing as a Free Lunch
In today's foreign trade industry, network connectivity (commonly known as "climbing the wall") is no longer just a technical topic; it is an essential infrastructure like water, electricity, and gas. To search for potential leads in Google's vast database, communicate instantly with Middle Eastern buyers via WhatsApp, build professional networks on LinkedIn, or track industry trends on YouTube, the first thing a newcomer does is look for a reliable "ladder" (VPN).
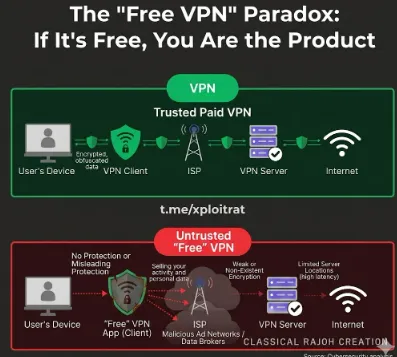
However, when you happily type "Free VPN" into a search box and download a tool with a crude icon and endless pop-ups, you might not realize that you are opening a door to an abyss. Remember the iron rule of the internet: If the product is free, you are the product.
I. The Cost of Free: Who is Paying for Your Traffic?
Maintaining a stable cluster of international dedicated servers involves massive annual costs for bandwidth, hardware maintenance, and R&D. If developers don't charge you, they must extract value through other channels:
-
Data Trafficking: Your Privacy is Their "Gold Mine" Free tools often deeply read your browsing history, contact information, and even account passwords. This data is packaged and sold to advertisers or even competitors in the foreign trade industry. You think you are discreetly developing clients, but your target list might already be on someone else's desk.
-
Bandwidth Hijacking: Your Computer Becomes a "Zombie" Some free tools use your computer as a node, borrowing your upstream bandwidth to accelerate other paid users or even launch DDoS attacks. This not only slows down your computer but could also involve your IP address in illegal activities, leading to your company's network being blocked by ISPs.
II. The Business Killer: Extremely Low and Unstable Connection Quality
Foreign trade business relies on timeliness and professionalism. When a free VPN "drops the chain" at critical moments, months of effort can vanish:
-
Communication Gaps: A video call with a client suddenly freezes, or a WhatsApp message is delayed for hours due to server congestion, making you look unprofessional.
-
Wasted Resources: Free lines are usually shared by thousands of people. These "dirty IPs" easily trigger Google's CAPTCHA mechanisms, trapping you in endless "click the carousel" verifications and destroying efficiency.
III. Hidden Minefields: Expensive Account Costs
For foreign trade professionals, LinkedIn, Facebook, and PayPal accounts are lifelines.
-
Banning Risks: Free tools frequently change IP addresses, which are often shared with spam accounts. When you use these "high-risk IPs" to log into business accounts, platform risk control systems easily flag your account as abnormal, leading to permanent bans. For an old LinkedIn account with thousands of contacts, this loss is irreplaceable.
-
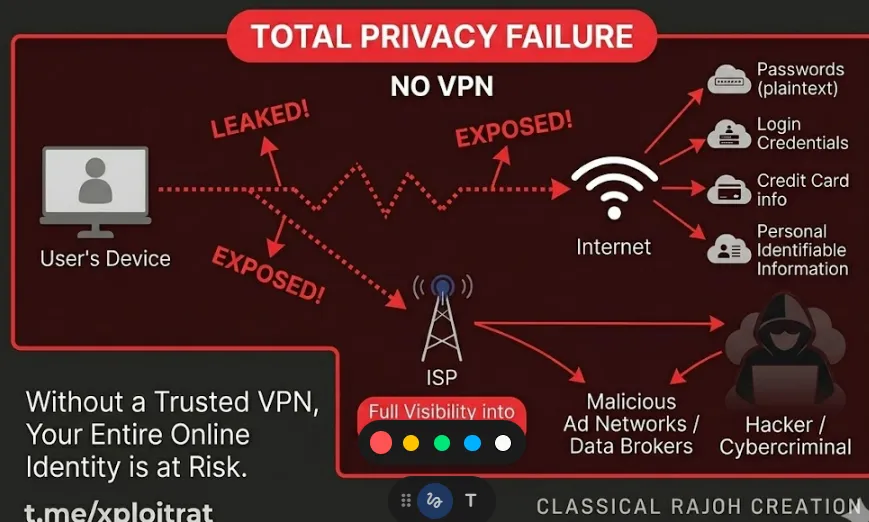
Financial Risks: If you log into online banking or handle payments while using a free VPN, your financial information may be exposed in plain text to the tool's developers.
Why Newbies Fall for "Free Ladders": 3 Core Reasons
Newcomers to the foreign trade industry often have limited knowledge of cross-border internet compliance and cybersecurity, making them easy targets for the hype of free VPN services. Fundamentally, they are misled by three key mindsets:
1. Limited Budget, Seeking Zero-Cost Cross-Border Internet Access
Most new practitioners have relatively low salaries, whether working part-time in foreign trade or joining a company that does not provide official cross-border network services. Unwilling to spend dozens or hundreds of yuan monthly on compliant services, they are easily tempted by the word "free," assuming they can solve essential work needs without cost—completely ignoring the hidden risks.
2. Information Gap, Unaware of Compliance and Security Bottom Lines
Newcomers generally lack understanding of China’s cybersecurity regulations and how unverified VPN services operate. They mistakenly believe any tool that connects to foreign networks, Google, or overseas social platforms is reliable. They cannot distinguish between legal, compliant channels and illegal tools, nor do they realize that using unauthorized VPN services without approval is itself a violation.
3. Impatience for Quick Results, Ignoring Long-Term Risks
New foreign trade practitioners are eager to develop clients and secure orders to prove themselves. Faced with slow internet or blocked access to overseas platforms, they only want a quick fix. They have no time or intention to verify whether a tool is safe or compliant. With a fluke mindset of "just use it first," they blindly download and use unregulated free VPN services from unknown sources.
Security Risks: You Think It's a Tool, but It's a "Backdoor"
Many new practitioners regard free VPNs as just internet tools, with nothing worse than slow speed and excessive ads. They have no idea that such unregulated tools essentially install an uncontrollable "backdoor" on your mobile phone or computer. All your data and privacy are being monitored and stolen in real time. The core security risks are as follows:
-
Complete Leakage of Private Data, No Privacy for Accounts and Passwords
Free VPNs provide no encryption protection. Providers can easily capture all your online records, including foreign trade email account passwords, Alibaba International / Amazon platform accounts, customer communication logs, bank card payment information, company customer data, etc. These sensitive data are either packaged and sold to cybercrime gangs or directly stolen. You are exposed while scammers are in the dark, leaving you completely defenseless.
-
Built-in Trojans and Viruses, Total Loss of Device Control
Most free VPN software bundles malicious trojans and virus plugins. After downloading and installation, viruses will automatically implant themselves in the device background, secretly reading your contacts, photo albums, call logs, and even remotely controlling your mobile phone and computer. They can tamper with files, delete customer data, and turn your device into a "bot".
-
DNS Hijacking and Traffic Monitoring, Commercial Information Eavesdropped
Criminals hijack your network traffic through free VPNs, tamper with webpage content, and even eavesdrop on your communications and email exchanges with overseas customers. Your core commercial information such as quotations, cooperation plans, and customer contact details is likely to be directly intercepted by competitors, and customers you have worked hard to follow up will be snatched instantly.
-
Illegal Risks: Crossing the Legal Red Line
According to the Cybersecurity Law of the People’s Republic of China and the Interim Provisions for the Administration of International Networking of Computer Information Networks, no organization or individual may establish or use illegal channels for international networking without permission. Using unregulated free VPNs without approval is illegal. Minor violations may result in warnings or network disconnection, while serious cases face fines and even criminal liability. New foreign trade practitioners must not take chances.
Real-Life Case Studies of Consequences
Many newbies in foreign trade only care about “being able to connect” when choosing network tools. In fact, poor network environments hide huge risks that can destroy an entire career. Below are two practical cases based on real backgrounds.
Case 1: Hard-Won Clients “Hijacked” — Email Backdoor & Fund Theft
Case Recap
Xiao Wang, a new foreign trade employee, used a so-called “free forever” VPN to log into his company email for convenience. After three months of tough negotiations, a major Brazilian client was ready to sign a contract, with a 50,000 USD deposit confirmed.
However, right after Xiao Wang sent the official Proforma Invoice (PI), the client suddenly “disappeared”. Two weeks later, Xiao Wang anxiously contacted the client via LinkedIn, only to be shocked:
“I transferred the deposit to your ‘new account’ ten days ago!”
In-Depth Analysis: How the Trap Happened
-
Credential Leakage
Free tools often intercept data through mirror sites or Man-in-the-Middle (MITM) attacks. Xiao Wang’s email username and password were stored in plaintext or easily decrypted form on unsafe public servers. -
Silent Monitoring
After gaining access, hackers did not change the password immediately. Instead, they set up “auto-forwarding” rules. Every email Xiao Wang sent was visible to hackers in real time. -
Precise Hijacking
Hackers imitated Xiao Wang’s tone and sent a fake email just before payment, claiming:
“Company financial audit: original account suspended. Please transfer to this offshore account.”
Due to an unstable network, Xiao Wang missed abnormal login alerts.
Chain Hazards
-
Financial Loss: Client deposit was scammed, causing heavy foreign exchange losses for the company.
-
Reputation Collapse: The client believed the company had poor management and even suspected collusion between Xiao Wang and the scammers. The cooperation ended completely.
-
Career Crisis: Xiao Wang faced severe accountability from the company, with early-career trust hitting rock bottom.
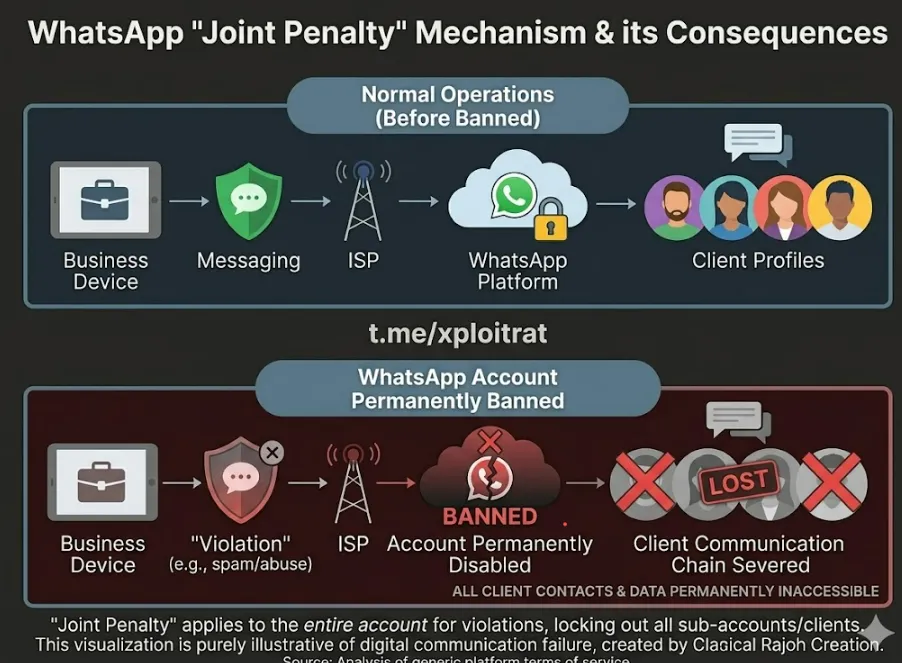
Case 2: WhatsApp Account Permanently Banned — Clients Lost Under “Joint Penalty” Mechanism
Case Recap
Xiao Xin, a new employee, mainly developed the Southeast Asian market via WhatsApp. Since the company did not provide a dedicated network, Xiao Xin used a free VPN.
One Monday morning, when opening the app as usual, the screen clearly showed:
“Your phone number is banned from using WhatsApp.”
Not only the new account, but also the previous account with over 50 potential clients and chat records became completely inaccessible.
In-Depth Analysis: How the Trap Happened
-
Extremely Low IP Reputation
Free VPNs share overused IPs, which have long been marked as “high-risk spam sources” by Meta (WhatsApp’s parent company). -
“Joint Penalty” Punishment
Once connecting to such an IP, the system judges the operating environment as abnormal. Even sending only a few messages can trigger detection or direct banning. -
Linked Bans
Bans usually target device ID and network environment. Switching to a new account under the same network still results in instant bans.
Chain Hazards
-
Private Traffic Cutoff: WhatsApp is a core communication channel. Banning wipes out all previous communication, sample confirmations, and client habits.
-
Communication Breakdown: Ongoing orders are easily lost to competitors as clients cannot reach the salesman.
-
Device “Blacklisted”: Frequent bans mark the device’s hardware fingerprint. Later, even with a legitimate network, stable accounts are extremely hard to maintain on that device.
Three Survival Tips for New Foreign Trade Practitioners
-
Reject “Unverified Cheap Tools”
Free services are often the most expensive. If your company does not provide a proper network, subscribe to legitimate, dedicated, high-reputation professional network services at your own cost.
-
Enable Two-Factor Authentication
For Gmail, Outlook, or corporate email, always turn on 2FA. Even if passwords leak, hackers cannot log in without a dynamic verification code.
-
Retain Clients Through Multiple Channels
Never rely on WhatsApp alone. Build a multi-channel matrix:
Email + LinkedIn + WhatsApp + WeChat / Skype
Ensure you can reconnect with clients within 5 minutes via backup methods if any channel fails.
Business Impact: Don’t Let Cheap Tools Ruin Your Hard-Won Development
Foreign trade relies on stability, trust, and efficiency. Every shortcoming of free VPNs strikes directly at the core pain points of foreign trade operations:
-
Extremely unstable network, disrupted client communication
Free VPNs suffer from slow speeds and frequent disconnections. Sudden network drops during video conferences, email sending, or inquiry replies make you appear unprofessional and unreliable to clients, directly losing potential customers.
-
Abnormal IP addresses, mass account bans
Free VPNs use chaotic, shared IP addresses, which are easily flagged as malicious by Google, overseas social media, and cross-border e-commerce platforms. This results in direct bans of emails, stores, and social accounts, which are difficult to recover through appeals. -
Data loss, wasted early efforts
Trojans and viruses can alter or delete customer data, quotations, and product documents. Your carefully compiled customer resources and development materials can be erased overnight. Reorganizing them wastes time and effort, missing the best development window.
Business Trap: The "Monetization Tactics" Behind Free Services
There is no truly free internet service. Free VPN providers are not running a charity. Their monetization methods are far more concealed and unethical than you imagine:
-
Stealing and selling data
This is their core way of profiting. They collect your account passwords, customer information, and business data, then sell them to cybercrime gangs or competitors for huge profits.
-
Forced bundled ads and malware
They push fraudulent ads and malicious software in the background, tricking you into downloading paid useless services or even redirecting you to phishing websites, leading to direct financial loss. -
Luring paid upgrades to exploit users
They attract users with “free” promises, then intentionally limit speed and disconnect frequently to force you into paid upgrades. Even after upgrading, there is still no security guarantee—you spend money but keep the risks. -
Secret mining to damage hardware
Some free VPNs run hidden mining programs in the background, occupying your device’s memory and computing power. This causes phones and computers to lag, overheat, and greatly shortens their lifespan.
Must-See for New Foreign Trade Practitioners:
Compliant, Safe & Low-Cost Alternatives
Cross-border internet access is essential for foreign trade, but compliance is always the top priority. Newcomers must never use illegal free VPN services. Here are several compliant, secure and low-cost alternatives suitable for different budgets and scenarios, safe for daily use:
-
Top Pick for Individuals & Newcomers:
Compliant Internet Services from Licensed Carriers
Contact the three major official telecom operators directly: China Mobile, China Unicom, and China Telecom. Ask about international dedicated lines or compliant cross-border internet packages designed for foreign trade and business use.
Personal plans usually cost around tens of yuan per month, with high cost-performance, full compliance, stable speed and no security risks. Ideal for new individual practitioners or small teams. -
Must-Have for Enterprises & Teams:
Professional Cross-Border Network Services for Foreign Trade
For corporate team use, choose professional cross-border network providers that are properly registered with MIIT and hold an Internet Value-Added Telecommunications Business License, such as SD-WAN international private lines and enterprise-grade broadband for foreign trade.
These services offer dedicated IPs, stable connections and encrypted data, supporting all foreign trade scenarios including video conferences, platform operation and client development. Although costs are slightly higher, security and stability are guaranteed to avoid greater losses. -
Temporary Emergency Solution:
Compliant Overseas Proxies & Official Platform Direct Services
For temporary overseas access, you can use legitimate paid independent IP proxies, or the built-in cross-border services of official foreign trade platforms such as Alibaba International and Made-in-China.
This allows secure access to overseas client resources without extra network setup, completely avoiding illegal tools.
2026 Professional VPN/Acceleration Tool Recommendation Guide
To ensure business continuity, it is recommended to adopt a "Main + Backup" strategy.
Core Tool Comparison Table
|
Tool Name |
Core Advantage |
Target Audience |
Budget |
Technical Bar |
|
Extremely stable, industry benchmark |
Large enterprises, high-value pros |
High ($12-30/mo) |
Low (Plug & Play) |
|
|
Instant connection, flexible billing |
Newbies, SOHO, temporary backup |
Medium (Weekly/Monthly) |
Very Low |
|
|
Unlimited devices, high value |
Startup teams, multi-device use |
Low (Very low per person) |
Low |
|
|
Self-built Node |
Pure IP, high account weight |
TikTok/Social Media pros |
Low ($50+/year) |
High |
1. Astrill VPN (The Business Benchmark)

-
Position: The undisputed gold standard for stability and professional reliability in mainland China.
-
Proprietary Protocols: Utilizes StealthVPN and OpenWeb, which are specifically engineered to scramble packet headers and disguise VPN traffic as standard HTTPS/TLS web data, making it nearly invisible to Deep Packet Inspection (DPI).
-
VIP Add-ons: Offers dedicated "VIP" servers with optimized routing for Asia-Pacific traffic, ensuring lower latency during peak hours.
-
Pros: High Performance: Exceptional speeds for bandwidth-heavy tasks like 4K streaming and low-latency international video conferencing (Zoom/Teams).
-
Smart Mode: A sophisticated split-tunneling feature that accelerates browser traffic for international sites while allowing local Chinese apps (WeChat, Alipay) to use the direct local network.
-
Cons: Significantly higher price point than competitors and a strict one-device/limited-device policy.
2. LetsVPN (The Efficiency Solution)
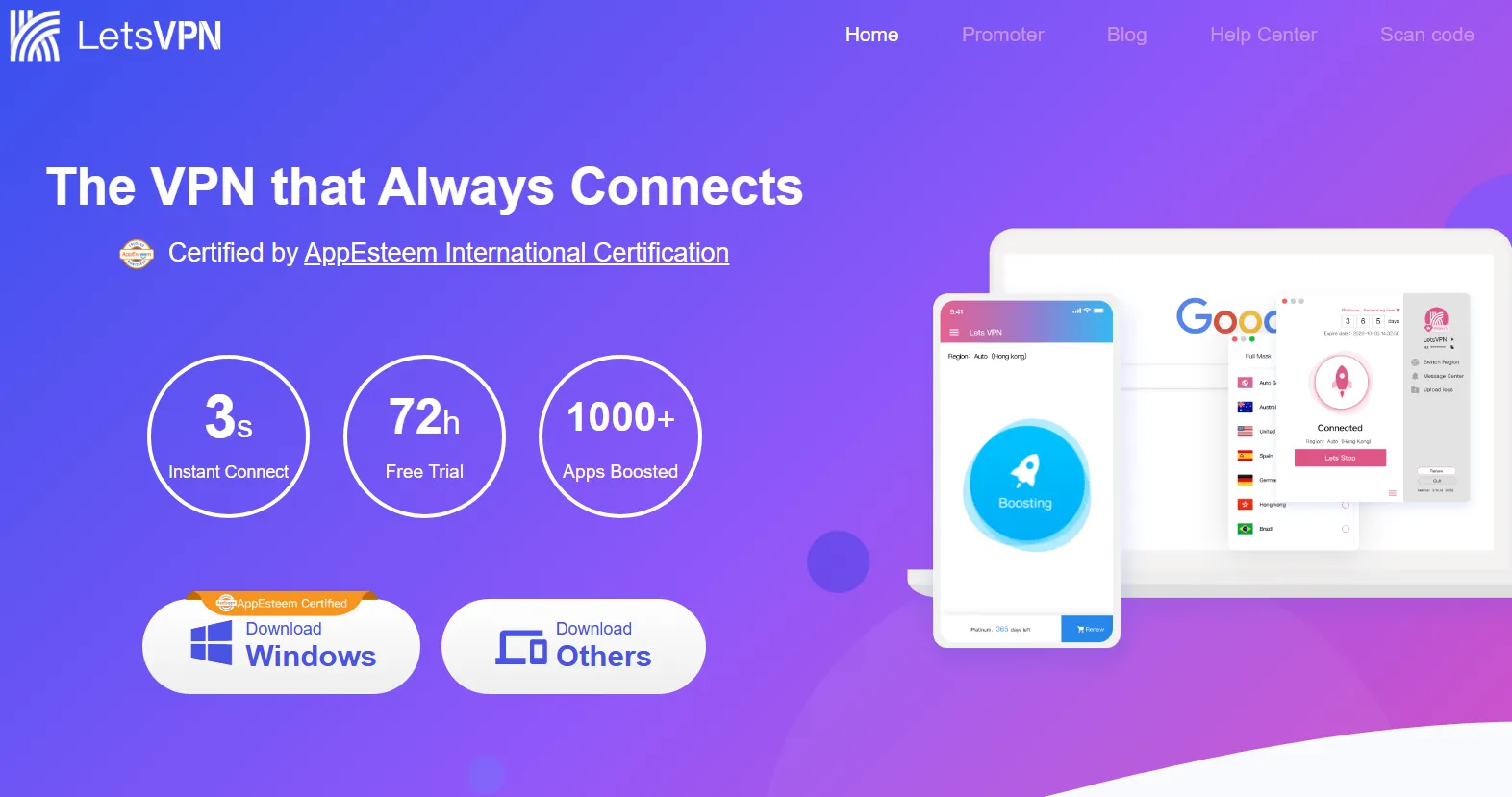
-
Position: The most popular "fool-proof" tool for 2024-2025, ideal for short-term travelers and non-technical users.
-
Operational Excellence: Known for its aggressive "cat-and-mouse" strategy, frequently updating its server IP addresses and obfuscation methods within minutes of a block.
-
Pros: Zero Learning Curve: A "one-click" interface that requires no manual configuration or server selection.
-
Billing Flexibility: Offers highly granular weekly and monthly billing cycles, making it perfect for temporary stays.
-
Resilience: Currently maintains one of the highest uptime records during sensitive "Red Weeks" or major regulatory periods in China.
-
Cons: Limited advanced features for power users; interface is functional but simplistic.
3. Surfshark (Value & Team Collaboration)
-
Position: The most budget-friendly major global VPN that maintains a consistent presence and specialized support for the Chinese market.
-
Security Suite: Beyond basic encryption, it integrates CleanWeb 2.0, which provides system-wide ad-blocking and proactive malware protection.
-
Pros: Unlimited Connectivity: Allows unlimited simultaneous connections on a single subscription, making it the ideal choice for small teams, startups, or large households.
-
No-Borders Mode: Automatically detects network restrictions and provides a curated list of servers specifically optimized to bypass the Great Firewall.
-
Dynamic MultiHop: Allows you to route your traffic through two different servers simultaneously for an extra layer of privacy.
-
Cons: Connection speeds may vary more than premium providers like Astrill.
4. Self-built Nodes (For Social Media/TikTok Ops)
-
Position: Advanced custom setups using Virtual Private Servers (VPS) such as BandwagonHost (CN2 GIA) or Vultr, running modern proxy protocols like VLESS, Trojan, or Hysteria2.
-
Technical Context: Unlike commercial VPNs that use shared IP pools, self-built nodes provide a dedicated environment that is less likely to be "blacklisted" by global platforms.
-
Pros: Exclusive Residential IPs: Crucial for "high-weight" account operations on TikTok, Amazon, Etsy, or ChatGPT. Using a dedicated IP prevents "chain-banning" where one user's bad behavior affects everyone on a shared VPN server.
-
Protocol Flexibility: Users can switch to the latest protocols (like Hysteria2) which are optimized for high-loss networks common in cross-border connections.
-
Cons: Requires significant technical knowledge to maintain; if the VPS IP is blocked, the user is responsible for the cost of changing it.
Core Operational Recommendations for Newcomers
To ensure the stability, compliance, and security of your foreign trade business, it is recommended that you make network environment setup a long-term practice. Below are the key operational suggestions for newcomers:
|
Dimension |
Key Essentials |
Practical Recommendations |
Reasons for Risk Avoidance |
|
Compliance |
Uphold the Bottom Line |
Only select network service providers with legal records; strictly prohibit the use of illegal or cracked VPNs (proxies). |
Avoid administrative penalties or business interruptions caused by compliance risks. |
|
Isolation |
Separate Office and Private Use |
Keep work emails and social media accounts (LinkedIn/FB, etc.) separate; ERP systems should only run on office networks; do not connect private networks to work devices. |
Prevent cross-infection or data leakage caused by impure personal network environments. |
|
IP Quality |
Independent Static IP |
Prioritize solutions that provide independent outbound IPs; avoid using cheap shared (public) IP nodes. |
Shared IPs often cause account risk control, weight reduction, or even permanent bans due to the "association effect." |
|
Account Protection |
Two-Factor Authentication (MFA) |
Critical platforms (Google, LinkedIn, Alibaba, etc.) must enable mobile/email 2FA; change high-strength passwords regularly. |
Even if the password is leaked, hackers cannot access the account without verification. |
|
Device Security |
Software Environment Purification |
Install genuine anti-virus software; prohibit downloading any cracked software, plugins, or scripts from unknown sources. |
Malicious plugins or Trojans may silently steal your customer information and transaction data. |
|
Data Backup |
Regular Archiving |
Regularly back up core materials such as business documents, customer correspondence, and PI/CI to cloud encrypted spaces or local cold storage. |
To deal with data loss risks caused by device damage, ransomware, or sudden environmental abnormalities. |
Summary Advice for Newcomers
-
Don’t be penny-wise and pound-foolish: Free or cheap network tools often mean insecurity and a high risk of account bans.
-
Stability over speed: For foreign trade professionals, a stable network and clean IP are more important than just fast download speeds.
-
Stay cautious: Never log into any business accounts on unfamiliar devices (such as public computers in hotels).
Hardware-Level Protection: VPN Routers
For SOHO (Small Office/Home Office) teams, we recommend hardware like GL.iNet GL-MT3000 (Beryl AX).
-
Benefits: It encrypts the entire office network at the source. This prevents "WebRTC leaks" at the browser level, which is a common way LinkedIn detects your true location even when a software VPN is active.
How to Verify Your Network Health: IP Reputation & Blacklists
Most foreign trade newbies assume that if Google opens, their VPN is "working." However, in 2026, social platforms use advanced IP Reputation Scoring to flag suspicious users before they even send their first inquiry. If your VPN assigns you a "dirty" IP address—one previously used by spammers or bots—your accounts are at immediate risk.
Step 1: Check Your "Fraud Score"
Before logging into LinkedIn or WhatsApp, use a professional diagnostic tool to see how the internet views your connection.
-
Scamalytics: https://scamalytics.com/ip
-
IPHub: https://iphub.info/
Step 2: Interpret the Data
Look for the Fraud Score or Risk Score (usually 0-100):
-
Score 0–10 (Safe): This is a high-quality, clean IP. It likely belongs to a reputable ISP or a premium VPN's dedicated server. Your B2B accounts are safe here.
-
Score 11–20 (Caution): You are on the radar. Avoid high-stakes activity like sending bulk LinkedIn connections or creating new ad accounts.
-
Score 21+ (Danger Zone): Disconnect immediately. A score above 20 indicates that this IP is flagged for fraudulent activity. Using this connection to access your business accounts is a "suicide mission" for your digital presence.
Step 3: Identify the "Connection Type"
If the tool lists your connection as "Business" or "Datacenter," platforms like Facebook will treat you with suspicion. The gold standard for 2026 is a "Residential" or "ISP" connection type, which mimics a real home user and is rarely blocked.
Conclusion: Foreign Trade is a Long Race — Don’t Lose the Whole for a Trifle
Foreign trade is never a get-rich-quick industry; it is a long race that relies on professionalism, stability, and attention to detail. A quality overseas client requires long-term follow-up and maintenance; a stable foreign trade career needs reputation built step by step; a substantial order demands countless days and nights of development and negotiation.
Never gamble your career prospects and business results to save a few dozen yuan per month on network costs. Seemingly free unregulated VPNs are actually the most costly traps. Compliant and secure internet access is the lowest-cost long-term investment for every foreign trade practitioner.
As a newcomer, keep to the bottom line from day one and avoid these hidden pitfalls. Focus your energy on client development, product learning, and business improvement — only then can you go further and steadier in this industry.
Frequently Asked Questions (FAQ)
Q: Why is the free VPN built into my phone also fast?
A: Short-term speed is just a bait. Developers usually allocate better resources to new users to keep you using it, so they can collect your data or show ads later. Once the user base grows, the speed will drop sharply.
Q: What should I do if I’ve already used a free VPN on my accounts?
A: 1. Stop using it immediately.2. Change passwords for all business-related accounts.3. Check for suspicious plugins or software on your system.4. Switch to reliable, paid nodes.
Q: My company doesn’t reimburse internet expenses. What should I choose?
A: Treat it as a career investment. For foreign trade professionals, network tools are as essential as your computer for making money. You should never cut costs here.
Q: Why do my clients say they didn’t receive my outreach emails after I used a free VPN?
A: Many email providers (such as Gmail, Outlook) are extremely sensitive to IPs from known free VPNs. If your login IP has a bad reputation, your emails will be automatically marked as spam or even blocked directly.
Q: Can unknown tools steal my customer information?
A: Yes, it’s very possible. A VPN is essentially a relay station. If the tool you use has no encryption or is malicious, your unencrypted communication with clients (inquiry details, draft quotations, contact information) can be fully intercepted and read on the relay server.
Q: Can free VPNs cause viruses or data leaks on my computer?
A: Many free VPN installers bundle Trojans or malicious software. They may monitor your keystrokes in the background to steal bank accounts, payment passwords, and login credentials for internal company systems.
Q: If it’s free, how do the developers make money?
A: There is no such thing as a free lunch. Servers cost a lot for bandwidth and electricity. Unknown free tools usually profit in these ways:
-
Selling your data: Recording your browsing habits, login info, and even payment details to sell to advertisers or hackers.
-
Injecting ads: Frequently showing malicious ads or forcing redirects.
-
Bandwidth sharing: Your device may be used as part of a botnet, attacking others using your bandwidth, causing lag and even legal risks.