In this digital age, data privacy faces unprecedented threats, and among the biggest challenges are the intelligence-sharing alliances secretly established by various governments. If you care about your online privacy and security, the "Five Eyes," "Nine Eyes," and "Fourteen Eyes" Alliances are a crucial consideration when selecting a Virtual Private Network (VPN) that cannot be avoided.
This article will reveal the truth about these alliances and guide you on how to choose a VPN that best protects your privacy based on their jurisdiction.
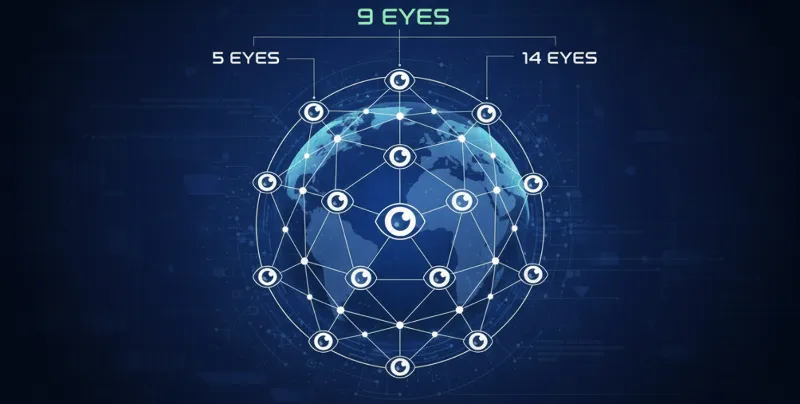
"Five Eyes" (FVEY), "Nine Eyes," and "Fourteen Eyes" are common names for international intelligence-sharing agreements. They are essentially cooperative mechanisms where member states mutually collect, analyze, and share large-scale surveillance data.
The Origin of the "Five Eyes" Alliance (FVEY)
The Five Eyes Alliance is the oldest and most influential of the three groups. Its origins trace back to 1946, after World War II, when the UK and the US signed the UKUSA Agreement to share Signals Intelligence (SIGINT). Over time, Canada, Australia, and New Zealand joined, formally establishing the Five Eyes Alliance.
-
Primary Purpose: To collect and share SIGINT from global communications (such as internet activity, phone calls, and emails). Initially targeting Cold War objectives, it has now evolved into a massive global surveillance network.
The Expansion: Nine and Fourteen Eyes
With the increased demand for global counter-terrorism and cybersecurity cooperation, the Five Eyes Alliance gradually expanded its scope of intelligence sharing to more countries. However, the intelligence access and depth of sharing for these new countries vary.
-
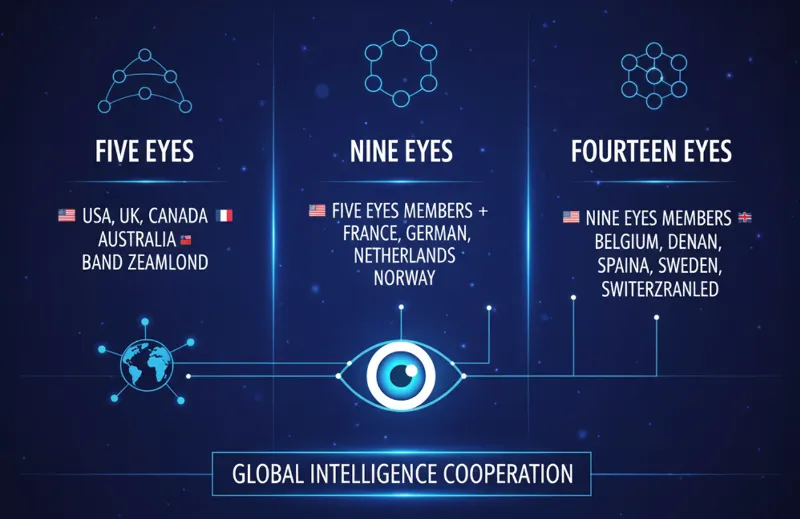
Nine Eyes (9 Eyes): Adds four partner countries to the Five Eyes. These countries contribute and receive some intelligence, but access to the core surveillance network is restricted.
-
Fourteen Eyes (14 Eyes) / SIGINT Seniors Europe: Further expands on the Nine Eyes, involving looser cooperation, usually exchanging intelligence only in specific areas (such as counter-terrorism or cybersecurity).
Understanding which countries belong to these alliances is vital, because if your VPN company is registered in one of these nations, your data could be legally mandated to be recorded and shared.
|
Alliance Name |
Involved Countries |
Cooperation Depth |
Privacy Risk Level |
|
Five Eyes (FVEY) |
🇺🇸 US, 🇬🇧 UK, 🇨🇦 Canada, 🇦🇺 Australia, 🇳🇿 New Zealand |
Core members, full sharing of classified intelligence, joint surveillance programs (e.g., ECHELON, PRISM). |
Extremely High |
|
Nine Eyes |
Five Eyes + 🇩🇰 Denmark, 🇫🇷 France, 🇳🇱 Netherlands, 🇳🇴 Norway |
Close cooperation, contribute and receive intelligence, but restricted access to core data. |
High |
|
Fourteen Eyes |
Nine Eyes + 🇧🇪 Belgium, 🇩🇪 Germany, 🇮🇹 Italy, 🇪🇸 Spain, 🇸🇪 Sweden |
Loose cooperation, exchange limited to specific security domains. |
Medium-High |
These intelligence-sharing alliances pose a profound threat to individual privacy, centered on a clever legal circumvention mechanism and boundless data collection scope.
3.1 Legal Loopholes: Bypassing Domestic Privacy Protection
Five Eyes member states typically have domestic privacy laws designed to protect their own citizens from warrantless government surveillance. However, the genius of the alliance lies in creating a "backdoor" to circumvent these restrictions:
-
Ally Monitoring: An intelligence agency in one country (e.g., the US NSA) typically cannot monitor its own citizens without due legal process, but it can ask an alliance partner's intelligence agency (e.g., the UK GCHQ) to conduct the surveillance.
-
Intelligence Data Repatriation: The partner country, after collecting data on the target citizen, can legally share it back with the requesting country.
Through this "mutual monitoring" mechanism, the alliance successfully bypasses the legal restrictions of their respective countries, making mass surveillance without the user's knowledge or consent possible. The data collected can even be shared with law enforcement, bypassing the legal safeguards users are entitled to, such as a search warrant required for data acquisition.
3.2 Types of Data Collected and Surveillance Targets
The Five Eyes Alliance (especially the US and UK) operates several massive, global intelligence collection programs such as ECHELON, PRISM, and XKeyscore, designed to continuously capture the following highly sensitive personal information:
-
Digital Footprints and Online Behavior (Internet Activity)
This includes users' web browsing history, detailed search queries, and file download records. Additionally, all online transactions, purchase behavior, and activity data from emails and social media platforms are within their scope of monitoring. -
Traditional Communication Metadata (Telephony and Messaging)
Through mass surveillance and metadata analysis of telephone networks, the alliance can track: the numbers of the caller and recipient, precise call times, duration, and geographical location. Concurrently, metadata from SMS and MMS messages are comprehensively recorded. -
Geographical Location and Travel Trajectories (Location and Travel Data)
Collection methods encompass real-time GPS signal tracking, mobile cell tower data, airline booking details, visa application information, and footage from public and private surveillance cameras, thereby constructing a complete personal movement history. -
Details of Economic Activity (Financial Transactions)
Through cooperation with banks, payment processing systems, and the SWIFT international money transfer network, the alliance monitors users' credit card spending records, cross-border fund movements, and cryptocurrency wallet transaction activity. -
Penetration of Encrypted Communications (Encrypted Communications)
Despite the use of end-to-end encrypted applications like WhatsApp, Signal, and Telegram, the alliance still attempts to gain access to these encrypted messages, iMessage communications, and even user files and backups stored in cloud services by leveraging decryption programs like Bullrun/Edgehill, as well as implanting backdoors, exploiting zero-day vulnerabilities, or using secret subpoenas.
3.3 The Expansion and Impact of Surveillance Scope
-
Global Data Capture: This surveillance is not limited to the citizens of member states. Your data, even an email merely passing through an alliance country's server, can be intercepted and collected by programs like GCHQ's "Tempora," making the impact global.
-
Data Sharing Beyond Fourteen Eyes: The reach of intelligence sharing extends far beyond the "Fourteen Eyes" members. Data can be sold or shared with even more allied countries. The Five Eyes Alliance is known to cooperate with other nations such as Israel, Japan, Singapore, and South Korea, further expanding its surveillance and data influence.
A VPN's main function is to encrypt your internet traffic and hide your real IP address. However, if your VPN company is registered in a "Five Eyes" alliance country, its No-Logs Policy can be instantly invalidated by a mandatory government request, rendering your protection useless.
VPN Risk in Alliance Countries
If a VPN company is headquartered in a Five, Nine, or Fourteen Eyes country, it may face these risks:
-
Mandatory Data Logging: Despite claiming "No-Logs," the government can use secret subpoenas or National Security Letters to force the company to start recording user data and prohibit the company from disclosing this action (a "gag order").
-
Physical Seizure: In some countries, intelligence agencies have the right to directly seize VPN servers and obtain all data on those servers.
-
Legal Pressure: Even if the company strictly enforces a no-logs policy, long-term legal pressure from the government can significantly increase operational difficulty.
How to Choose a "Safe" VPN?
To minimize the risks associated with these intelligence-sharing alliances, you should focus on the following points when choosing a VPN:
-
Avoid Alliance Jurisdictions
Prioritize companies headquartered in countries/regions outside the alliance scope and without mandatory data retention laws.
|
Recommended Safe Jurisdiction |
Notable VPN Examples |
|
Panama |
NordVPN |
|
British Virgin Islands (BVI) |
ExpressVPN |
|
Switzerland |
Proton VPN |
|
Malta |
Surfshark |
|
Romania |
CyberGhost |
-
Independently Audited "No-Logs" Policy
Any VPN can claim to be "No-Logs." However, a No-Logs policy only becomes credible if it has been independently audited by internationally renowned third-party organizations such as KPMG, PricewaterhouseCoopers (PwC), or Deloitte, and the audit report is made public. -
RAM-Only Servers (Volatile Memory Servers)
Many top-tier VPN providers have transitioned to using RAM-Only servers (servers that run exclusively in volatile memory). This means that all data is completely wiped on every restart, making it impossible to write user activity logs to the hard drive, thus ensuring a no-logs state at the physical level. -
Transparency Reports and Judicial History
A responsible VPN company will regularly publish Transparency Reports, detailing how many data requests they have received from government or law enforcement agencies, and how much data they provided (usually zero, as they have no logs to provide). Also, check their history for any record of seizures or cooperation with intelligence agencies.
Top-Tier No-Logs VPN Providers Summary:
NordVPN (Jurisdiction: Panama)
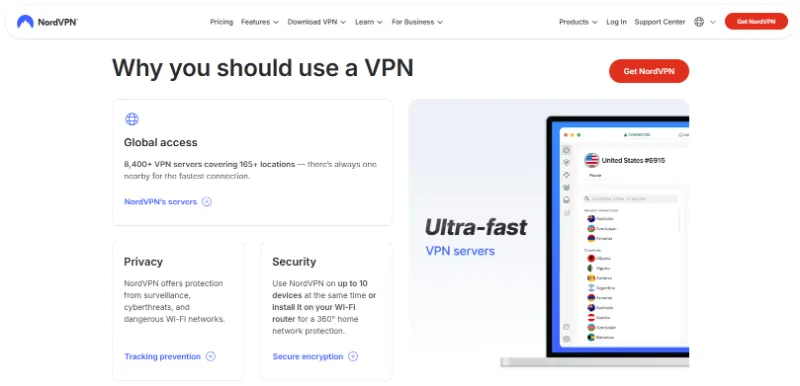
-
Scale & Speed: Features over 8,400+ ultra-fast servers across 165 countries.
-
Streaming Capability: Highly reliable for unblocking major streaming services with excellent performance.
-
All-in-One Security Suite: Includes Threat Protection (antivirus, ad-blocking, malware defense) and specialized security features like Double VPN (multi-hop).
ExpressVPN (Jurisdiction: British Virgin Islands)
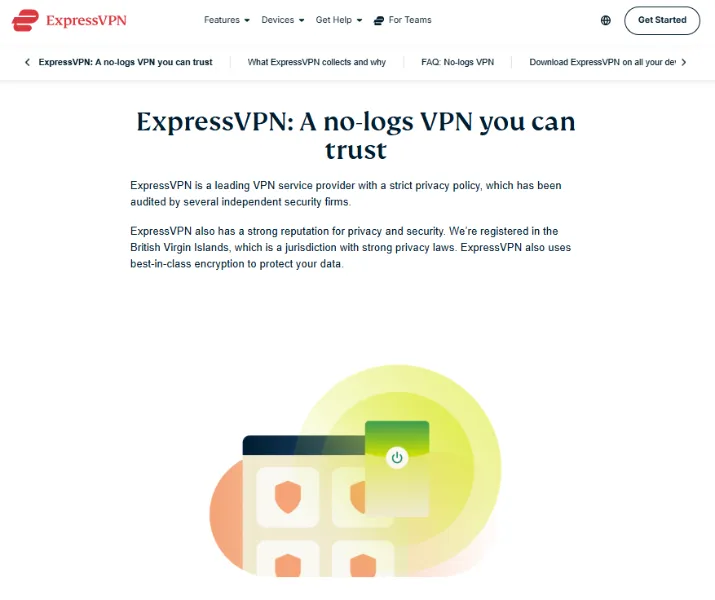
-
Scale & Speed: Servers in 105 countries, utilizing the proprietary Lightway protocol for optimized speed and security.
-
Streaming Capability: An ideal choice for global connectivity and reliable streaming unblocking.
-
Core Security Guarantee: Industry-leading TrustedServer technology (RAM-Only servers) ensures data is never written to hard drives.
Proton VPN (Jurisdiction: Switzerland)
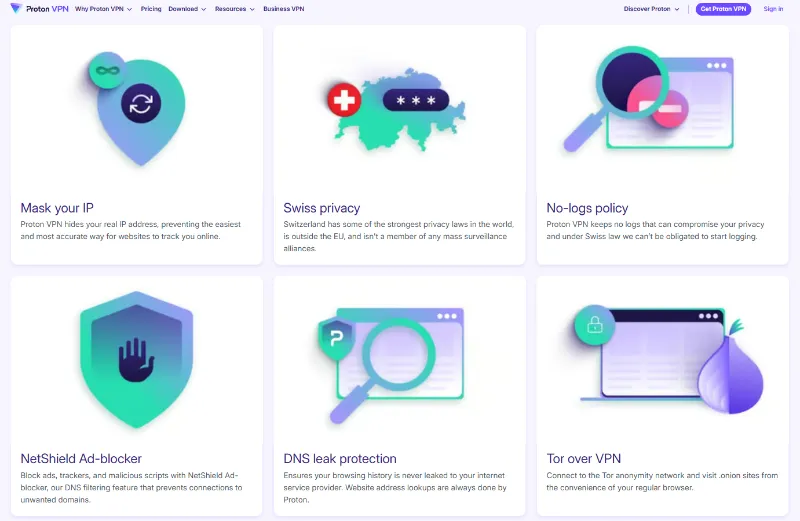
-
Scale & Speed: Operates over 4,800 servers, with VPN Accelerator technology capable of increasing long-distance connection speeds up to 400%.
-
Streaming Capability: Provides seamless and robust support for streaming services.
-
Ultimate Privacy & Ecosystem: Built on an open-source ethos, features Secure Core multi-hop routing, and includes a free encrypted email account (ProtonMail).
CyberGhost VPN (Jurisdiction: Romania)
-
Scale & Speed: Boasts a massive network of 11,690+ servers specifically optimized for high-speed streaming and gaming.
-
Streaming Capability: Servers are optimized for high-speed streaming and gaming performance.
-
Features & Automation: Offers unique automation features, such as automatic VPN activation upon detecting an unsecure Wi-Fi network.
While completely avoiding the global surveillance network is extremely challenging, adopting multiple protective measures can significantly enhance your digital privacy and data security. Here are key strategies for countering surveillance by the Five Eyes and other alliances:
5.1 Deploying a VPN with a Strict Zero-Logs Principle
-
Encrypted Connection and Identity Hiding: Ensure all your network traffic is routed through high-strength encryption, and use a VPN to hide your true IP address, making it difficult for external snoopers to read and track your activity.
-
Selecting Key Features: Be sure to choose a VPN service with independent jurisdiction, strict third-party audits, and RAM-Only server technology to physically guarantee no retention of user activity logs.
5.2 Implementing End-to-End Communication Encryption
-
Ensuring Information Confidentiality: Whether for instant messaging or email, prioritize platforms that offer End-to-End Encryption (E2EE) (e.g., Signal, ProtonMail, or Tutanota). E2EE ensures that only the sender and the intended recipient have the decryption keys, thus preventing any intermediary (including the service provider) from reading your communication content.
5.3 Avoiding Services in High-Risk Jurisdictions
-
Prudently Evaluating Providers: When choosing cloud storage, email, or various software services, carefully assess where their headquarters are located. Given the Five Eyes Alliance's legal loopholes, lean towards companies registered in countries with strong privacy protection laws (such as Switzerland, Panama) to mitigate the risk of forced data sharing.
5.4 Adopting Privacy-Optimized Browsing Tools
-
Browser and Search Engine Choices: Abandon traditional browsers and search engines that track user behavior. It is recommended to use privacy-focused browsers like Brave, which integrates default ad and tracker blocking, and pair it with privacy-focused search engines like DuckDuckGo or Brave Search, which commit to not recording search history.
5.5 Utilizing the Tor Network for Deep Anonymity
-
Multi-Layer Routing Anonymization: For scenarios requiring the highest level of anonymity, you can utilize the Tor network. It greatly increases the difficulty of tracking by randomly routing traffic through multiple relay nodes globally with multi-layer encryption. Note that the cost of high anonymity is typically slower connection speed.
5.6 Cautiously Managing Smart Device Monitoring Risks
-
Potential Surveillance Tools: Modern smart devices such as smart home assistants, smart TVs, and wearables are potential data collection points. They can gather a wide range of information, from voice recordings to health data.
-
Physical and Software Management: Limit these devices' permissions to process sensitive information, and when not in use, reduce the risk of exploitation by disabling microphones and cameras, or even physically disconnecting the power.
5.7 Strengthening Basic Digital Hygiene and Security Measures
-
Timely Patching of Vulnerabilities: Ensure operating systems, devices, and all applications are promptly updated to prevent security vulnerabilities from being used for monitoring or intrusion.
-
Security Foundation: Use a professional password manager to generate and store complex and unique passwords to prevent credential leaks. Simultaneously, enable Two-Factor Authentication (2FA) for all important accounts to provide an extra layer of security.
The Five, Nine, and Fourteen Eyes Alliances represent one of the greatest threats to global citizens' privacy. When choosing a VPN, you are not just buying a service; you are choosing a form of digital sovereignty.
By deeply understanding the operation of the intelligence alliances, selecting a VPN registered outside the alliance jurisdiction, and combining this with the proactive defense strategies in Section 5 (such as end-to-end encryption, using privacy browsers, and strengthening digital hygiene), you can build a multi-layered defense system to maximize the assurance that your online activities will not become part of these global surveillance networks. In the digital age, actively defending your privacy freedom is paramount.
Q1: What is the difference between a VPN and the Tor Network, and which one should I use?
|
Feature |
VPN (Virtual Private Network) |
Tor (The Onion Router) |
|
Encryption Layers |
Single layer (some offer Double VPN) |
Multi-layered (usually three layers) |
|
Anonymity |
Offers high-level anonymity, but depends on the No-Logs policy |
Offers the highest level of anonymity by routing traffic through multiple encrypted relays |
|
Speed |
Generally faster, suitable for streaming and downloading |
Significantly slower, as traffic passes through multiple nodes |
|
Coverage |
Encrypts all internet traffic (browsers, applications, etc.) |
Primarily used for browser traffic (though configuration exceptions exist) |
|
Risk |
Jurisdiction risk; risk if the VPN retains logs |
Exit node risk; data is decrypted at the exit node and may be monitored |
Recommendations
-
If you seek security, speed, and streaming capability, choose a trustworthy No-Logs VPN.
-
If you seek extreme anonymity and do not mind the speed compromise, use Tor.
-
Best Practice: To balance security and anonymity, you can use Tor Over VPN (connect to a VPN first, then access the network through the Tor browser). This adds a layer of protection, preventing your ISP from knowing you are accessing the Tor network.
Q2: Can my government or Internet Service Provider (ISP) know that I am using a VPN?
Yes, they can usually detect that you are using a VPN, but they cannot know what you are doing while connected to the VPN.
-
How They Detect: VPNs often use known IP address ranges. When your ISP sees all your traffic encrypted and directed to a server in a data center, they may suspect you are using a VPN.
-
Privacy Protection: Nevertheless, because your traffic is protected by the VPN's high-strength encryption, your government or ISP cannot peek into the websites you visit, your search history, or your real IP address.
-
Bypassing Detection: In some countries with strict VPN restrictions (like China), you can use Obfuscated Servers. These servers disguise VPN traffic, making it look like regular HTTPS traffic, thereby bypassing Deep Packet Inspection (DPI) system blocks.
Q3: How likely is a VPN provider to be forced to hand over user data?
This depends entirely on the VPN company's jurisdiction and its logging policy:
-
High Risk (Five Eyes Countries): If a VPN is headquartered in a Five Eyes country like the US or UK, the local government can use a court subpoena or National Security Letter (often accompanied by a "gag order") to compel the company to hand over data.
-
Low Risk (Safe Jurisdiction): If a VPN is headquartered in a country without data retention laws, such as Panama or the British Virgin Islands, local law does not require it to record or surrender user data.
-
The Key is "No-Logs": Even if the government issues a mandatory order, if the VPN truly maintains a "Zero-Logs" policy (i.e., it has not recorded any connection or activity data), then it will have "no data to hand over." This is why choosing an independently audited No-Logs VPN is crucial.
Q4: What is a RAM-Only Server, and why is it safer?
-
A RAM-Only Server (or pure memory server) is an advanced VPN infrastructure technology that operates exclusively on volatile memory (RAM).
-
Data Erasure Guarantee: Unlike traditional servers that write data to a hard drive, all data on a RAM-Only Server (including any session logs or configurations) is completely wiped upon every restart.
-
Physical Protection: This means that even if a server is physically seized by an intelligence agency, no user-identifiable activity logs will be found on the hard drive. It provides a physical-level "No-Logs" guarantee and is considered one of the safest server architectures available today.